 Online gambling was the top industry sector targeted by ransomware last year, according to a new report.
Online gambling was the top industry sector targeted by ransomware last year, according to a new report.
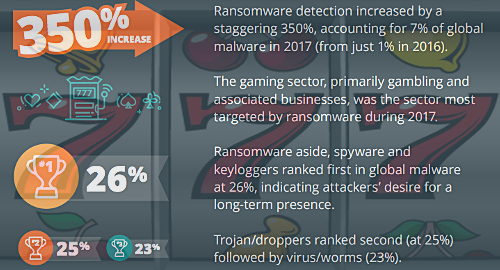
The 2018 Global Threat Intelligence Report by global cyber resilience firm NTT Security found that the volume of ransomware – the malicious blocking of access to data unless payment is made – surged 350% in 2017, accounting for 7% of all global malware attacks last year.
The gaming industry was the target of 20% of all ransomware attacks last year, higher than the business & professional services (17%), health care (12%), manufacturing (12%) and technology (11%) sectors. Two types of ransomware, the Locky trojan and WannaCry worm, accounted for 45% and 30%, respectively, of all such attacks in 2017.
NTT described ransomware as the “weapon of choice” targeting gambling operators in the Europe, Middle East and Africa (EMEA) region, which accounted for 36% of all such attacks in 2017.
Gambling sites are also traditionally the top sector targeted by distributed denial of service (DDoS) attacks, evidence of which was on full display this past week at US-facing online poker site Americas Cardroom.
A new Kapersky Lab study showed DDoS attacks had undergone a “significant” increase in the first quarter of 2018 compared to Q4 2017. Worse, the number of ‘amplified’ attacks, which dramatically ramp up the data volume hurled at targeted sites, “picked up momentum” in Q1.
Kapersky reported that long-duration DDoS attacks were also on the rise, including a 297-hour attack against a single target, the longest sustained attack since 2015.
In a rare bit of positive news, DDoS attacks in Europe have reportedly decreased by 60% since crimefighters Europol dismantled the WebStresser DDoS-for-hire service last month. A multi-nation operation dubbed ‘Power OFF’ resulted in the arrests of WebStresser’s administrators and the seizure of server infrastructure in the Netherlands, Germany and the US.
WebStresser was considered the largest such service, with over 136k registered users who paid as little as €14.99 to access the tools of their nefarious trade, and was reportedly the source of some 4m DDoS attacks since the site’s launch in 2015. However, the respite is likely to be brief as rival DDoS services rush to fill the void.