 Malicious cyberattacks against online gambling sites soared during the pandemic lockdown as scammers looked to take advantage of the sites’ increased popularity.
Malicious cyberattacks against online gambling sites soared during the pandemic lockdown as scammers looked to take advantage of the sites’ increased popularity.
Technology analytics firm Neustar Security recently released its Cyber Threats & Trends Report: Jan-Jun 2020, which details a 151% surge in the number of distributed denial of service (DDoS) attacks in the first half of 2020 compared to the same period last year.
Worse, these attacks are getting more powerful and lasting longer. While attacks at the lower end of the scale involving 5 Gigabits (Gbps) or lower per second were up over 200% year-on-year – and such attacks represented over 70% of observed attacks – those at the other extreme (involving 100 Gbps or more) were up around 275%.
The longest attack duration this year was five days and 18 hours, the longest Neustar has ever observed, while the largest individual attack size was a whopping 1.17 Terabits per second, the largest that Neustar has ever mitigated (although Amazon Web Service reported a client being hit by a 2.3Tbps attack). The average attack size rose by 1Gbps year-on-year to 12Gbps.
Attacks also rose in intensity, from an average of 2 million packets per second (Mpps) to 3Mpps. The most intense attack Neustar mitigated in H1 2020 was 350Mpps, 81% higher than H1 2019’s most intense attack, although the company notes that an attack of over 800Mpps was observed this year, beating the previous record of 500Mpps.
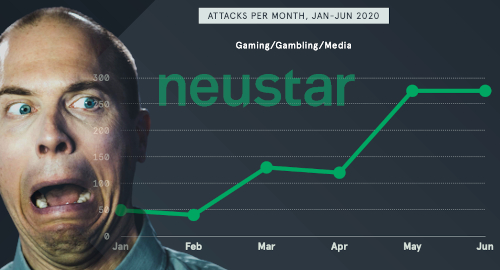
Internet service providers, registries and hosting sites endured over 500 attacks per month in June, a 102% increase from January. The gaming/gambling/media category saw fewer attacks, but experienced a far more dramatic increase. From less than 50 attacks in February, the number more than doubled in March then spiked to around 275 by May and stayed at that level in June.
The bulk of attacks (43%) involve only two threat vectors, with diminishing numbers for three vector attacks (35%), four (16%) and over four (1%). The widespread dissemination of DDoS amplification vectors and the prevalence of DDoS-for-hire services have played major roles in the rise of more sophisticated attacks.
In March, as pandemic lockdowns took hold around the world, the Cybercrime Centre at Cambridge University in the UK observed dramatic spikes in attacks using a particular booster/stressor firm, in part due to a similarly large spike in new users signing up for this service.
With the pandemic not expected to go away anytime soon and online activity remaining at an elevated level, malicious attacks will likely only increase. As an old TV cop used to say, let’s be careful out there.